|
This document describes version 5 of Unblu. If you’re using the latest major version of Unblu, go to the documentation of the latest version. The support period for version 5 ended on 22 November 2021. We no longer provide support or updates for this version. You should upgrade to the latest version of Unblu. |
Compromising the Agent Session
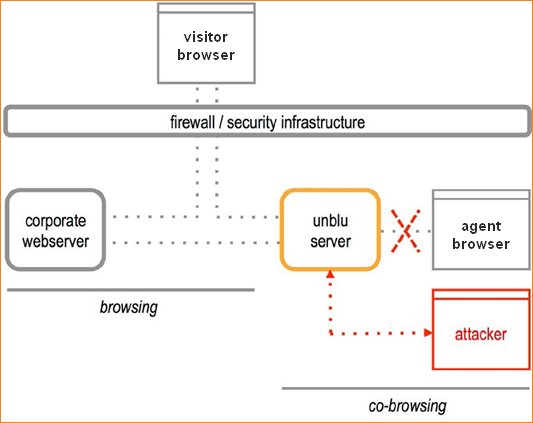
This attack assumes that the attacker already has access to your company’s IT infrastructure, for example as an office worker. The attacker tries to gain access to the agent’s session, in order to learn account numbers, passwords, or to execute tasks on the customer’s web page.
First, the attacker needs access to the IT infrastructure, and more specifically, to a network that handles Unblu connections. Also, an agent might try to hack into another agent’s connection, so he or she could perform malicious actions undetected.
Once in the network, the attacker might try to access the network traffic addressed to the agent. If your network is not secured, this can be done using standard network tools. The attacker can then see the same information as the agent. Using more sophisticated methods, the attacker may insert information of their own into the network traffic, which may include commands to the customer’s web page.
How we Prevent the Agent Session from being Compromised
-
Unblu uses your existing internal network structure and security for co-browsing.
-
We recommend that you use an encrypted connection from the Unblu server to the agent. This makes it impossible to listen to the network communications, or to modify network communications.
-
Unblu uses two independent session IDs: One for the session between the server and the visitor, and another for the session between the server and the agent. If an attacker learns one ID, he or she cannot use it to guess the other.
-
The session ID is independent of the number the customer types-in to connect to the server. If an attacker intercepts the PIN, they cannot use it to guess the session ID.
-
The PIN that the customer types into the login field to establish the connection is discarded after the login. An attacker cannot use it to make another connection, or to take over an existing connection.
-
You can restrict the information that an agent sees and the action the agent can take. We recommend you limit both of these to what is necessary for effective relationship management.
| Depending on your infrastructure and security precautions, it may be simple for a skilled person to listen to your network traffic, especially if you use wireless networks. We strongly recommend that you secure the traffic between the Unblu server and the agent. |
Can the Agent Session be Compromised in a Cloud Setup?
In a cloud setup, agents use a standard HTTPS connection to communicate with the collaboration server. This means that all traffic is automatically secured, so there is no possibility that unsecured information is transmitted over an internal network.